On May 11, 2026, at approximately 19:20 UTC, a self-propagating supply chain worm dubbed `Mini Shai-Hulud` injected malicious code into ten official releases across five @tanstack/* packages within a six-minute window, and is actively spreading across projects. The TanStack Router framework is a cornerstone of the modern React ecosystem, used by hundreds of thousands of projects worldwide.
Unlike traditional supply chain attacks that compromise a single package via a stolen credential, Mini Shai-Hulud is a worm: it steals GitHub tokens, npm tokens, and CI/CD secrets from its victims, then uses those tokens to compromise additional packages, spreading itself autonomously through the ecosystem. The attack was first detected by Stepecurity's OSS Package Security Feed, and the incident is still active at the time of writing.
Attack Overview
The attack exploits a fundamental trust assumption in modern CI/CD pipelines: that a package published by a legitimate account through a legitimate pipeline is safe. Mini Shai-Hulud invalidates that assumption entirely.
- Initial vector: The worm gained access to a CI/CD pipeline token for a TanStack maintainer account. The exact initial compromise vector is still under investigation, but the worm's defining behavior is that it harvests secrets during the npm install phase of any pipeline that install san infected package.
- Payload injection: Ten malicious versions of official @tanstack/* packages, including @tanstack/router-generator@1.166.48 — were published to the npm registry carrying a 2.3 MB obfuscated credential-stealing payload. All ten versions appeared as legitimate releases from the official TanStack organization.
- Credential harvesting: The payload silently exfiltratesGitHub tokens, npm publish tokens, and any other CI/CD secrets present in the build environment during npm install. No user interaction or post-install script approval is required.
- Self-propagation: Harvested npm tokens are used by the worm to publish additional poisoned releases of other packages the compromised account has access to, spreading the infection without any further attacker intervention. This is what makes Shai-Hulud categorically more dangerous than a conventional package takeover.
- Speed: All ten malicious versions were published in under six minutes, before any human reviewer could intervene.
Affected Packages
The following @tanstack packages and versions are confirmed malicious. Do not install or upgrade to these versions.
@tanstack/router-generator@1.166.45
@tanstack/router-generator@1.166.48
@tanstack/router-core@1.169.8
@tanstack/router-utils@1.161.14
@tanstack/virtual-file-routes@1.161.13
@tanstack/react-router@1.169.8Additional affected packages and versions are being tracked in real time on the StepSecurity OSS Package Security Feed (app.stepsecurity.io/oss-security-feed). The list is expected to grow as the incident evolves. Treat any @tanstack/*version with suspicion; if a malicious version is found, assume compromise and rotate credentials.
How to Check with Arnica
Arnica customers can search their SBOM for impacted @tanstack packages directly from the platform. We have added the Mini Shai-Hulud campaign to Arnica's celebrity vulnerability database, allowing you to identify all affected package versions across your entire codebase instantly, including transitive dependencies and container images.
To find affected packages in your SBOM:
- Navigate to the SBOM view in Arnica.
- Use the advanced search filter and select "@tanstackShai-Hulud (May 2026)" from the dropdown.
- Arnica will surface every repository and container image in your organization that references an affected version, across all connected SCM platforms.
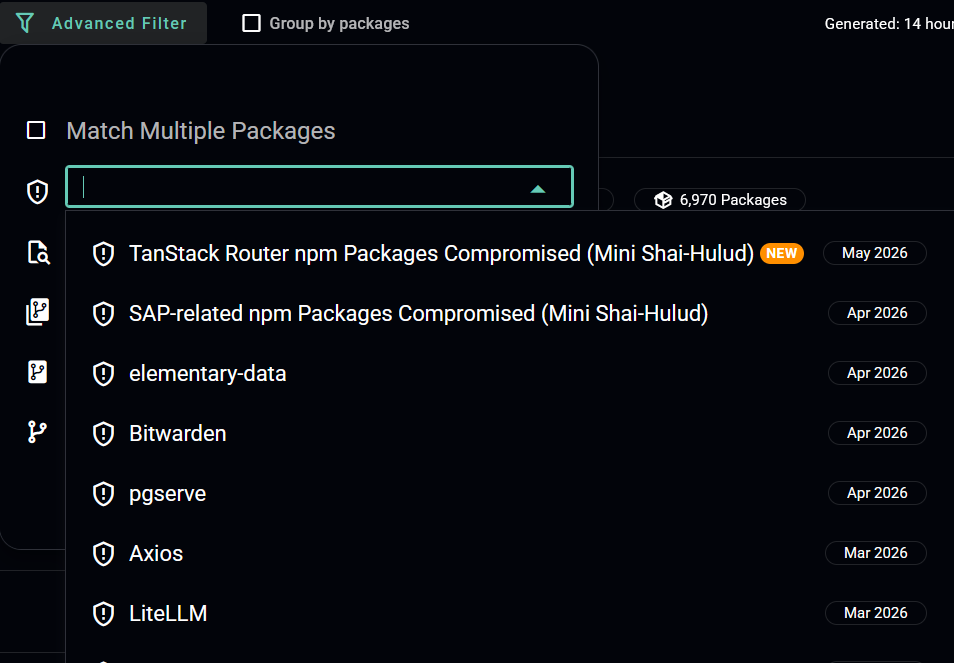
Because this worm spreads by compromising CI/CD pipelines, it is especially important to check not just your direct dependencies but also any internal packages that may have been published by a pipeline that previously installed an infected @tanstack version. Arnica's SBOM coverage across both source repositories and container images helps you close that gap quickly.
Arnica customers have the visibility needed to identify exposure to this campaign today. If you're not yet an Arnica customer and want to check whether your organization is affected, get started with Arnica for free at app.arnica.io.
Reduce Risk and Accelerate Velocity
Integrate Arnica ChatOps with your development workflow to eliminate risks before they ever reach production.